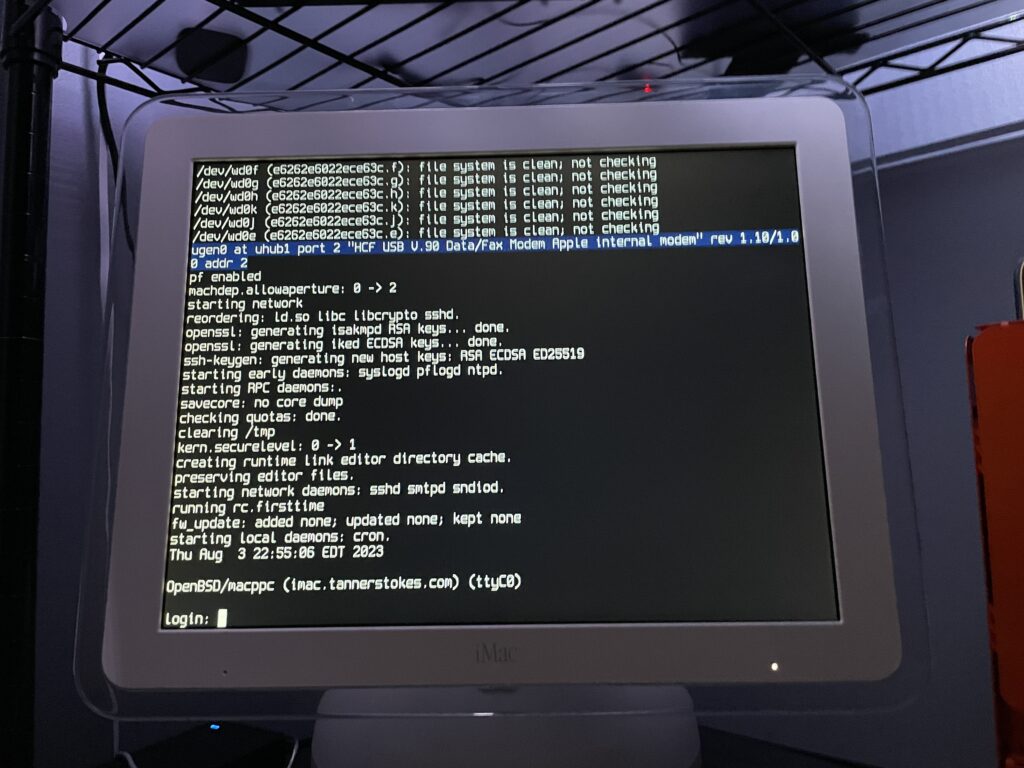
Fun fact: You can put the latest version of OpenBSD on a PPC 32-bit processor like the G4. Fun to dual boot with Mac OS 9 if you want a modern, secure computer!
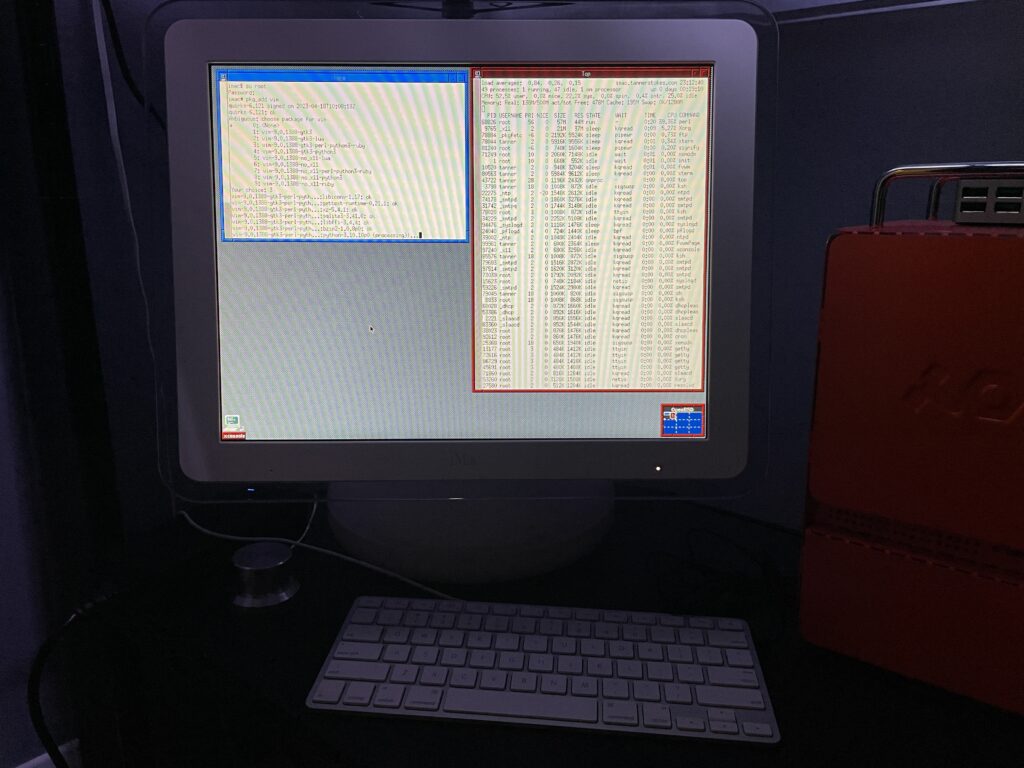
Some notes
The OpenBSD docs are really good and thorough. Open Firmware needs some tweaking if you want to boot directly into OpenBSD, so this is what I did after booting into it with command+option+o+f:
setenv auto-boot? True
setenv boot-device hd:,ofwboot
reset-allI failed to get a USB install working
Initially I didn’t want to mess with the internal drive of the iMac since I had both Mac OS 9 and Mac OS X installed, so I tried to install to a USB drive. Although the installation succeeded (albeit extremely slowly due to USB 1.1), the boot into the system failed due to the following error:
panic: rootfilesystem has size 0
Looking at the trace of the kernel boot process it was evident why: Even though we installed the OS to sd0 (the mounted USB device), the kernel kept trying to mount wd0 which is the internal IDE drive.
I tried what I knew:
- Tweaking the
boot-devicevariable in Open Firmware - Using a different USB slot
- Booting into the recovery kernel (
bsd.rd) and mounting the USB to see if I could tweakfstab
Supposedly if we get to the boot prompt we can pass a -a flag for the root device (docs), but I couldn’t figure out how to get there.
Ultimately I decided to install OpenBSD to the main internal drive for now. If I get a hankering for Mac OS 9 I still have the trusty Power Mac G4.
The best setup will eventually be a dual or triple-boot. Trying to make the super-slow USB drive work is probably a terrible idea unless we plan to run it in a ramdisk mode the entire time.
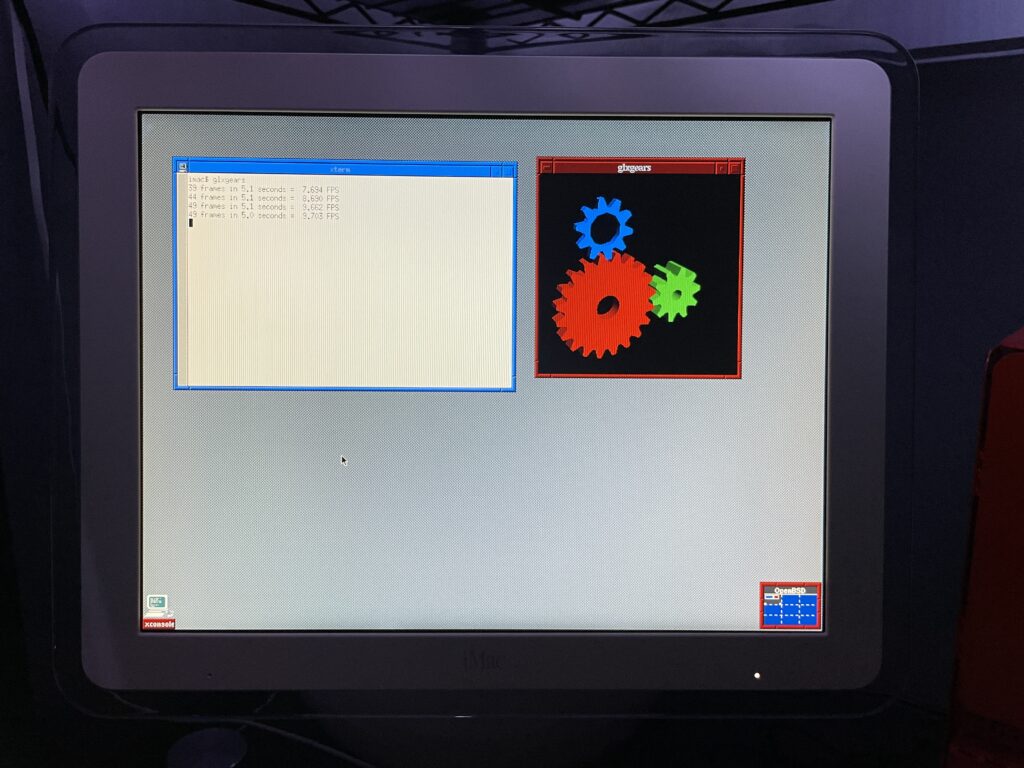
The graphics driver kinda works
As you can see from the glxgears output above graphics are not accelerated. I’ve mostly played with the machine over SSH in a headless state so this hasn’t bothered me too much. I did glance at dmesg and saw that the expected driver, nv, was loaded and detected the card so I’m not totally sure what’s happening. I’m having flashbacks of when I used to spend hours tweaking xorg.conf and that may be on the horizon again.
If just running the console we still want the screen to sleep and I found I needed to make a couple tweaks for that to work.
First I needed to shut down X Windows:
rcctl stop xenodm
Then I needed to disable output activity from waking the screen:
display.outact=off
After that the screen would shut off after however many milliseconds were set for display.screen_off.
Copying over /etc/examples/wsconsctl.conf to /etc/ is a great starter config.
Turn-key graphics support depends on the model
If you’re running a G4 iMac 15″ that’s less than 1GHz, you have the GeForce2 MX which doesn’t have support out of the box via the nouveau driver. This means an unaccelerated graphics environment, low framerates, and sometimes a console that has inverted colors making it really hard to use.
The GeForce4 MX integrated on the 1GHz 15″ model and most of the 17″ iMacs is supported.
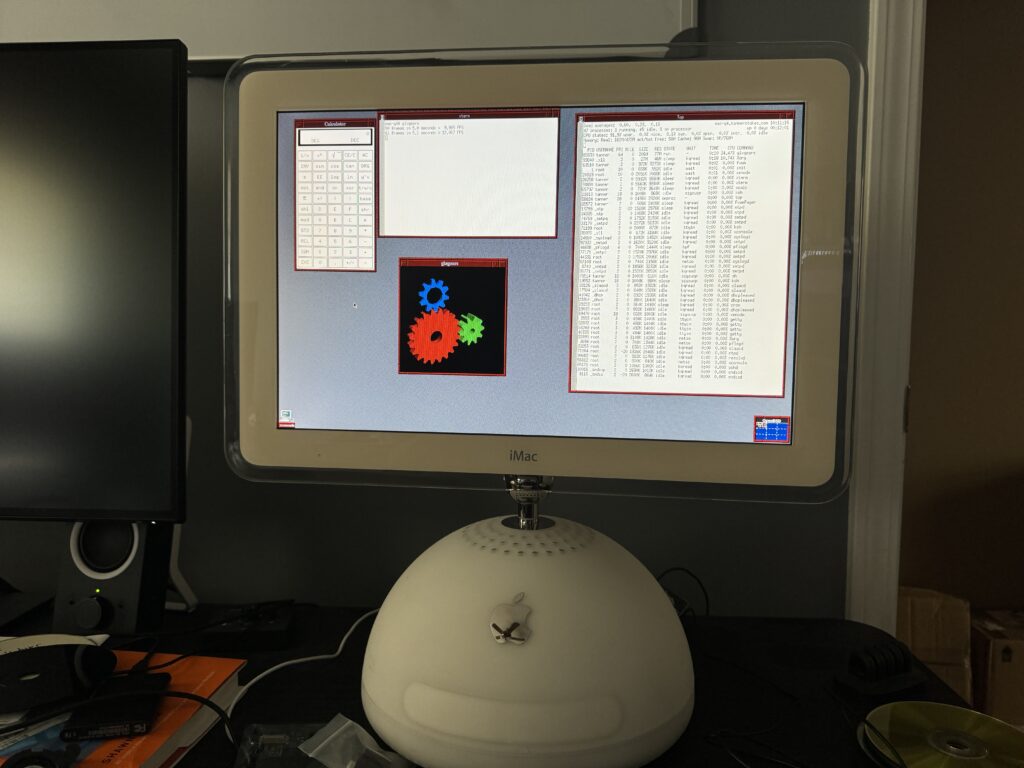
glxgears at a blazing 12FPS.Oh yeah, it runs DOOM
(Very poorly, presumably until the graphics driver is tweaked)
Running Chocolate Doom was painful. Even the setup utility had a good second or so input lag!